- Engineering Mathematics
- Discrete Mathematics
- Operating System
- Computer Networks
- Digital Logic and Design
- C Programming
- Data Structures
- Theory of Computation
- Compiler Design
- Computer Org and Architecture
- Computer Network Tutorial

Basics of Computer Network
- Basics of Computer Networking
- Introduction to basic Networking Terminology
- Goals of Networks
- Basic characteristics of Computer Networks
- Challenges of Computer Network
- Physical Components of Computer Network
Network Hardware and Software
- Types of Computer Networks
- LAN Full Form
- How to Set Up a LAN Network?
- MAN Full Form in Computer Networking
- MAN Full Form
- WAN Full Form
- Introduction of Internetworking
- Difference between Internet, Intranet and Extranet
- Protocol Hierarchies in Computer Network
- Network Devices (Hub, Repeater, Bridge, Switch, Router, Gateways and Brouter)
- Introduction of a Router
- Introduction of Gateways
- What is a network switch, and how does it work?
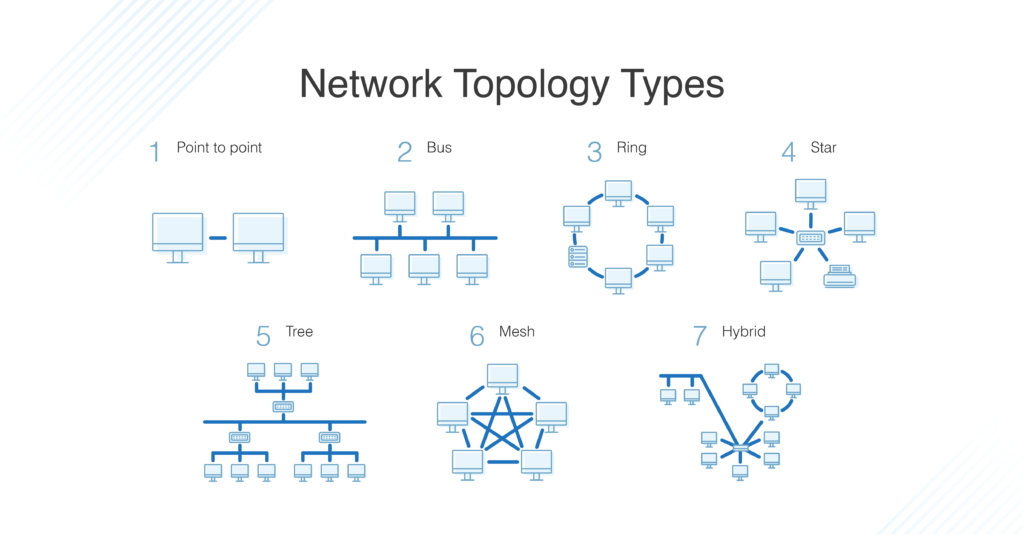
Network Topology
- Types of Network Topology
- Difference between Physical and Logical Topology
- What is OSI Model? - Layers of OSI Model
- Physical Layer in OSI Model
- Data Link Layer
- Session Layer in OSI model
Presentation Layer in OSI model
- Application Layer in OSI Model
- Protocol and Standard in Computer Networks
- Examples of Data Link Layer Protocols
- TCP/IP Model
- TCP/IP Ports and Its Applications
- What is Transmission Control Protocol (TCP)?
- TCP 3-Way Handshake Process
- Services and Segment structure in TCP
- TCP Connection Establishment
- TCP Connection Termination
- Fast Recovery Technique For Loss Recovery in TCP
- Difference Between OSI Model and TCP/IP Model
Medium Access Control
- MAC Full Form
- Channel Allocation Problem in Computer Network
- Multiple Access Protocols in Computer Network
- Carrier Sense Multiple Access (CSMA)
- Collision Detection in CSMA/CD
- Controlled Access Protocols in Computer Network
SLIDING WINDOW PROTOCOLS
- Stop and Wait ARQ
- Sliding Window Protocol | Set 3 (Selective Repeat)
- Piggybacking in Computer Networks
IP Addressing
- What is IPv4?
- What is IPv6?
- Introduction of Classful IP Addressing
- Classless Addressing in IP Addressing
- Classful Vs Classless Addressing
- Classless Inter Domain Routing (CIDR)
- Supernetting in Network Layer
- Introduction To Subnetting
- Difference between Subnetting and Supernetting
- Types of Routing
- Difference between Static and Dynamic Routing
- Unicast Routing - Link State Routing
- Distance Vector Routing (DVR) Protocol
- Fixed and Flooding Routing algorithms
- Introduction of Firewall in Computer Network
Congestion Control Algorithms
- Congestion Control in Computer Networks
- Congestion Control techniques in Computer Networks
- Computer Network | Leaky bucket algorithm
- TCP Congestion Control
Network Switching
- Circuit Switching in Computer Network
- Message switching techniques
- Packet Switching and Delays in Computer Network
- Differences Between Virtual Circuits and Datagram Networks
Application Layer:DNS
- Domain Name System (DNS) in Application Layer
- Details on DNS
- Introduction to Electronic Mail
- E-Mail Format
- World Wide Web (WWW)
- HTTP Full Form
- Streaming Stored Video
- What is a Content Distribution Network and how does it work?
CN Interview Quetions
- Top 50 Networking Interview Questions (2024)
- Top 50 TCP/IP interview questions and answers
- Top 50 IP addressing interview questions and answers
- Last Minute Notes - Computer Networks
- Computer Network - Cheat Sheet
- Network Layer
- Transport Layer
- Application Layer
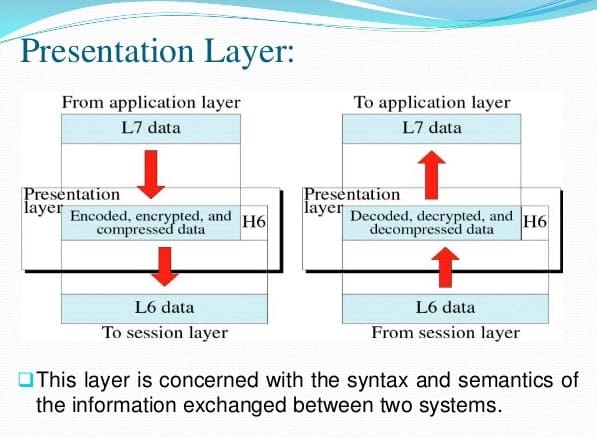
Prerequisite : OSI Model
Introduction : Presentation Layer is the 6th layer in the Open System Interconnection (OSI) model. This layer is also known as Translation layer, as this layer serves as a data translator for the network. The data which this layer receives from the Application Layer is extracted and manipulated here as per the required format to transmit over the network. The main responsibility of this layer is to provide or define the data format and encryption. The presentation layer is also called as Syntax layer since it is responsible for maintaining the proper syntax of the data which it either receives or transmits to other layer(s).
Functions of Presentation Layer :
The presentation layer, being the 6th layer in the OSI model, performs several types of functions, which are described below-
- Presentation layer format and encrypts data to be sent across the network.
- This layer takes care that the data is sent in such a way that the receiver will understand the information (data) and will be able to use the data efficiently and effectively.
- This layer manages the abstract data structures and allows high-level data structures (example- banking records), which are to be defined or exchanged.
- This layer carries out the encryption at the transmitter and decryption at the receiver.
- This layer carries out data compression to reduce the bandwidth of the data to be transmitted (the primary goal of data compression is to reduce the number of bits which is to be transmitted).
- This layer is responsible for interoperability (ability of computers to exchange and make use of information) between encoding methods as different computers use different encoding methods.
- This layer basically deals with the presentation part of the data.
- Presentation layer, carries out the data compression (number of bits reduction while transmission), which in return improves the data throughput.
- This layer also deals with the issues of string representation.
- The presentation layer is also responsible for integrating all the formats into a standardized format for efficient and effective communication.
- This layer encodes the message from the user-dependent format to the common format and vice-versa for communication between dissimilar systems.
- This layer deals with the syntax and semantics of the messages.
- This layer also ensures that the messages which are to be presented to the upper as well as the lower layer should be standardized as well as in an accurate format too.
- Presentation layer is also responsible for translation, formatting, and delivery of information for processing or display.
- This layer also performs serialization (process of translating a data structure or an object into a format that can be stored or transmitted easily).
Features of Presentation Layer in the OSI model: Presentation layer, being the 6th layer in the OSI model, plays a vital role while communication is taking place between two devices in a network.
List of features which are provided by the presentation layer are:
- Presentation layer could apply certain sophisticated compression techniques, so fewer bytes of data are required to represent the information when it is sent over the network.
- If two or more devices are communicating over an encrypted connection, then this presentation layer is responsible for adding encryption on the sender’s end as well as the decoding the encryption on the receiver’s end so that it can represent the application layer with unencrypted, readable data.
- This layer formats and encrypts data to be sent over a network, providing freedom from compatibility problems.
- This presentation layer also negotiates the Transfer Syntax.
- This presentation layer is also responsible for compressing data it receives from the application layer before delivering it to the session layer (which is the 5th layer in the OSI model) and thus improves the speed as well as the efficiency of communication by minimizing the amount of the data to be transferred.
Working of Presentation Layer in the OSI model : Presentation layer in the OSI model, as a translator, converts the data sent by the application layer of the transmitting node into an acceptable and compatible data format based on the applicable network protocol and architecture. Upon arrival at the receiving computer, the presentation layer translates data into an acceptable format usable by the application layer. Basically, in other words, this layer takes care of any issues occurring when transmitted data must be viewed in a format different from the original format. Being the functional part of the OSI mode, the presentation layer performs a multitude (large number of) data conversion algorithms and character translation functions. Mainly, this layer is responsible for managing two network characteristics: protocol (set of rules) and architecture.
Presentation Layer Protocols : Presentation layer being the 6th layer, but the most important layer in the OSI model performs several types of functionalities, which makes sure that data which is being transferred or received should be accurate or clear to all the devices which are there in a closed network. Presentation Layer, for performing translations or other specified functions, needs to use certain protocols which are defined below –
- Apple Filing Protocol (AFP): Apple Filing Protocol is the proprietary network protocol (communications protocol) that offers services to macOS or the classic macOS. This is basically the network file control protocol specifically designed for Mac-based platforms.
- Lightweight Presentation Protocol (LPP): Lightweight Presentation Protocol is that protocol which is used to provide ISO presentation services on the top of TCP/IP based protocol stacks.
- NetWare Core Protocol (NCP): NetWare Core Protocol is the network protocol which is used to access file, print, directory, clock synchronization, messaging, remote command execution and other network service functions.
- Network Data Representation (NDR): Network Data Representation is basically the implementation of the presentation layer in the OSI model, which provides or defines various primitive data types, constructed data types and also several types of data representations.
- External Data Representation (XDR): External Data Representation (XDR) is the standard for the description and encoding of data. It is useful for transferring data between computer architectures and has been used to communicate data between very diverse machines. Converting from local representation to XDR is called encoding, whereas converting XDR into local representation is called decoding.
- Secure Socket Layer (SSL): The Secure Socket Layer protocol provides security to the data that is being transferred between the web browser and the server. SSL encrypts the link between a web server and a browser, which ensures that all data passed between them remains private and free from attacks.
Please Login to comment...
Similar reads.

- 10 Best Todoist Alternatives in 2024 (Free)
- How to Get Spotify Premium Free Forever on iOS/Android
- Yahoo Acquires Instagram Co-Founders' AI News Platform Artifact
- OpenAI Introduces DALL-E Editor Interface
- Top 10 R Project Ideas for Beginners in 2024
Improve your Coding Skills with Practice
What kind of Experience do you want to share?
Presentation Layer: Protocols, Examples, Services | Functions of Presentation Layer
Presentation Layer is the 6th layer in the Open System Interconnection (OSI) model where all application programmer consider data structure and presentation, beyond of simply sending the data into form of datagram otherwise packets in between the hosts. Now, we will explain about what is presentation layer with its protocols, example, service ; involving with major functions of presentation Layer with ease. At the end of this article, you will completely educate about What is Presentation Layer in OSI Model without any hassle.
- What is Presentation Layer?
Definition : Presentation layer is 6th layer in the OSI model , and its main objective is to present all messages to upper layer as a standardized format. It is also known as the “ Translation layer “. This layer takes care of syntax and semantics of messages exchanged in between two communication systems. Presentation layer has responsible that receiver can understand all data, and it will be to implement all data languages can be dissimilar of two communication system.

Presentation layer is capable to handle abstract data structures, and further it helps to defined and exchange of higher-level data structures.
Presentation Layer Tutorial Headlines:
In this section, we will show you all headlines about this entire article; you can check them as your choice; below shown all:
- Functions of Presentation Layer
Protocols of Presentation Layer
- Example of Presentation Layer Protocols
Presentation Layer Services
Design issues with presentation layer, faqs (frequently asked questions), what is meant by presentation layer in osi model, what protocols are used in the presentation layer, can you explain some presentation layer examples, what are the main functions of the presentation layer, what are services of presentation layer in osi, let’s get started, functions of presentation layer.
Presentation layer performs various functions in the OSI model ; below explain each one –
- Presentation layer helps to translate from American standard code for information interchange (ASCII) to the extended binary code decimal interchange code (EBCDIC).
- It deals with user interface as well as supporting for several services such as email and file transfer.
- It provides encoding mechanism for translating all messages from user dependent format with common format and vice – versa.
- It’s main goal for data encryption and decryption of entire data before they are getting transmission over all common platforms.
- It provides data compression mechanism for source point to decrease the all bits which are transmitted. Due to this data compression system, user are able to transmit enlarge multimedia file at fastest file transfer rate.
- Due to use of Data Encryption and Decryption algorithm, presentation layer provides more network protection and confidentiality while transmission data over the entire network.
- This layer offers best flexibility for data translation for making connections with various kinds of servers , computers, and mainframes over the similar network.
- Presentation layer has responsible to fix all translations in between all network systems .
Presentation layer is used various protocols; below list is available –
- Multipurpose Internet Mail Extensions
- File Transfer Protocol
- Network News Transfer Protocol
- Apple Filing Protocol (AFP)
- Independent Computing Architecture (ICA), the Citrix system core protocol
- Lightweight Presentation Protocol (LPP)
- NetWare Core Protocol (NCP)
- Network Data Representation (NDR)
- Telnet (a remote terminal access protocol)
- Tox Protocol
- eXternal Data Representation (XDR)
- 25 Packet Assembler/Disassembler Protocol (PAD)
Example of Presentation Layer Protocols:
Here, we will discuss all examples of presentation layer protocols; below explain each one –
Multipurpose Internet Mail Extensions (MIME) : MIME protocol was introduced by Bell Communications in 1991, and it is an internet standard that provides scalable capable of email for attaching of images, sounds and text in a message.
File Transfer Protocol (FTP) : FTP is a internet protocol, and its main goal is to transmit all files in between one host to other hosts over the internet on TCP/IP connections.
Network News Transfer Protocol (NNTP) : This protocol is used to make connection with Usenet server and transmit all newsgroup articles in between system over internet.
Apple Filing Protocol (AFP ) : AFP protocol is designed by Apple company for sharing all files over the entire network .
Lightweight Presentation Protocol (LPP) : This protocol is used to offer ISO presentation services on top of TCP/IP based protocol stacks.
NetWare Core Protocol (NCP) : NCP is a Novell client server model protocol that is designed especially for Local Area Network (LAN). It is capable to perform several functions like as file/print-sharing, clock synchronization, remote processing and messaging.
Network Data Representation (NDR) : NDR is an data encoding standard, and it is implement in the Distributed Computing Environment (DCE).
Telnet (Telecommunication Network) : Telnet protocol was introduced in 1969, and it offers the command line interface for making communication along with remote device or server .
Tox : The Tox protocol is sometimes regarded as part of both the presentation and application layer , and it is used for sending peer-to-peer instant-messaging as well as video calling.
eXternal Data Representation (XDR) : This protocol provides the description and encoding of entire data, and it’s main goal is to transfer data in between dissimilar computer architecture.
25 Packet Assembler/Disassembler Protocol (PAD) : Main objective of this protocol is to obtain all data from group of terminal and allots the data into X. 25 packets.
Presentation layer provides several services like as –
- Data conversion
- Character code translation
- Compression
- Encryption and Decryption
- It helps to handle and maintain Syntax and Semantics of the message transmitted.
- Encoding data can be done as standard agreed like as String, double, date, and more.
- Standard Encoding can be done on wire.
Presentation Layer is the 6th layer in the Open System Interconnection (OSI) model that is the lowest layer, where all application programmer consider data structure and presentation, beyond of simply sending the data into form of datagram otherwise packets in between the hosts.
Presentation layer is used various protocols like as:
Yes! In this article, already we have been explained many examples of presentation layer; you can check them.
Presentation layer has a responsibility for formatting, translation, and delivery of the information for getting to process otherwise display .
Now, i hope that you have completely learnt about what is presentation layer with its protocols, example, service ; involving with major functions of presentation Layer with ease. If this post is useful for you, then please share it along with your friends, family members or relatives over social media platforms like as Facebook, Instagram, Linked In, Twitter, and more.
Also Read: Data Link Layer: Protocols, Examples | Functions of Data Link Layer
If you have any experience, tips, tricks, or query regarding this issue? You can drop a comment!
Related Posts

Layer 6 Presentation Layer
De/Encryption, Encoding, String representation
The presentation layer (data presentation layer, data provision level) sets the system-dependent representation of the data (for example, ASCII, EBCDIC) into an independent form, enabling the syntactically correct data exchange between different systems. Also, functions such as data compression and encryption are guaranteed that data to be sent by the application layer of a system that can be read by the application layer of another system to the layer 6. The presentation layer. If necessary, the presentation layer acts as a translator between different data formats, by making an understandable for both systems data format, the ASN.1 (Abstract Syntax Notation One) used.
OSI Layer 6 - Presentation Layer
The presentation layer is responsible for the delivery and formatting of information to the application layer for further processing or display. It relieves the application layer of concern regarding syntactical differences in data representation within the end-user systems. An example of a presentation service would be the conversion of an EBCDIC-coded text computer file to an ASCII-coded file. The presentation layer is the lowest layer at which application programmers consider data structure and presentation, instead of simply sending data in the form of datagrams or packets between hosts. This layer deals with issues of string representation - whether they use the Pascal method (an integer length field followed by the specified amount of bytes) or the C/C++ method (null-terminated strings, e.g. "thisisastring\0"). The idea is that the application layer should be able to point at the data to be moved, and the presentation layer will deal with the rest. Serialization of complex data structures into flat byte-strings (using mechanisms such as TLV or XML) can be thought of as the key functionality of the presentation layer. Encryption is typically done at this level too, although it can be done on the application, session, transport, or network layers, each having its own advantages and disadvantages. Decryption is also handled at the presentation layer. For example, when logging on to bank account sites the presentation layer will decrypt the data as it is received.[1] Another example is representing structure, which is normally standardized at this level, often by using XML. As well as simple pieces of data, like strings, more complicated things are standardized in this layer. Two common examples are 'objects' in object-oriented programming, and the exact way that streaming video is transmitted. In many widely used applications and protocols, no distinction is made between the presentation and application layers. For example, HyperText Transfer Protocol (HTTP), generally regarded as an application-layer protocol, has presentation-layer aspects such as the ability to identify character encoding for proper conversion, which is then done in the application layer. Within the service layering semantics of the OSI network architecture, the presentation layer responds to service requests from the application layer and issues service requests to the session layer. In the OSI model: the presentation layer ensures the information that the application layer of one system sends out is readable by the application layer of another system. For example, a PC program communicates with another computer, one using extended binary coded decimal interchange code (EBCDIC) and the other using ASCII to represent the same characters. If necessary, the presentation layer might be able to translate between multiple data formats by using a common format. Wikipedia
- Data conversion
- Character code translation
- Compression
- Encryption and Decryption
The Presentation OSI Layer is usually composed of 2 sublayers that are:
CASE common application service element
Sase specific application service element, layer 7 application layer, layer 6 presentation layer, layer 5 session layer, layer 4 transport layer, layer 3 network layer, layer 2 data link layer, layer 1 physical layer.
Please Whitelist This Site? I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :) If you like The TCP/IP Guide, please consider the download version . It's priced very economically and you can read all of it in a convenient format without ads. If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK. Thanks for your understanding! Sincerely, Charles Kozierok Author and Publisher, The TCP/IP Guide
The presentation layer is the sixth layer of the OSI Reference Model protocol stack, and second from the top. It is different from the other layers in two key respects. First, it has a much more limited and specific function than the other layers; it's actually somewhat easy to describe, hurray! Second, it is used much less often than the other layers; in many types of connections it is not required.
The name of this layer suggests its main function as well: it deals with the presentation of data. More specifically, the presentation layer is charged with taking care of any issues that might arise where data sent from one system needs to be viewed in a different way by the other system. It also takes care of any special processing that must be done to data from the time an application tries to send it until the time it is sent over the network.
Here are some of the specific types of data handling issues that the presentation layer handles:
The reason that the presentation layer is not always used in network communications is that the jobs mentioned above are simply not always needed. Compression and encryption are usually considered “optional”, and translation features are also only needed in certain circumstances. Another reason why the presentation layer is sometimes not mentioned is that its functions may be performed as part of the application layer.
The fact that the translation job done by the presentation layer isn't always needed means that it is common for it to be “skipped” by actual protocol stack implementations. This means that protocols at layer seven may talk directly with those at layer five. Once again, this is part of the reason why all of the functions of layers five through seven may be included together in the same software package, as described in the overview of layers and layer groupings .
- Introduction To Computer Networks
- Uses of Computer Networks
- Line Configuration
- Types of Network Topology
- Transmission Modes
- Transmission Mediums
- Bounded/Guided Transmission Media
- UnBounded/UnGuided Transmission Media
- Types of Communication Networks
- Connection Oriented and Connectionless Services
- Quality of Service(QoS)
- Network Layer
- IGMP Protocol
- Reference Models
- Digital Transmission
- Multiplexing
- Circuit-Switched
- Message-Switched Networks
- Packet Switching
- Error Correction
- Data Link Control
- Flow and Error
- Simplest Protocol
- Stop-and-Wait Protocol
- Go-Back-N Automatic Repeat
- Sliding Window Protocol
- HDLC Protocol
- Point-to-Point Protocol
- Multiple Access in DL
- Channelization Protocols
- Gigabit Ethernet
- Random Access Protocol
- Controlled Access Protocols
- Carrier Sense Multiple Access
- Transport Layer
- Telnet vs SSH
- UDP Protocol
- TCP - Protocol
- Introduction to Reference Models
- OSI Model: Physical Layer
- OSI Model: Datalink Layer
- OSI Model: Network Layer
- OSI Model: Transport Layer
- OSI Model: Session Layer
- OSI Model: Presentation Layer
- OSI Model: Application Layer
- The TCP/IP Reference Model
- Difference between OSI and TCP/IP Model
- Key Terms - Computer Network
- Session Layer
- Components of Computer Networks
- Features of Computer Network
- Protocols and Standards
- Connection Oriented and Connectionless
- OSI Vs TCP/IP
Presentation Layer
- HTTP Protocol
- FTP Protocol
- SMTP Protocol
- POP Protocol
- SNMP Protocol
- Electronic Mail
- MIME Protocol
- World Wide Web
- DNS Protocol
In this tutorial, we will be covering the Presentation layer of the OSI reference model in Computer Networks.
The presentation layer is layer-6 of the OSI reference model . This layer mainly responds to the service requests from the application layer(that is layer-7) and issues the service requests to layer-6 that is (the session layer).
This layer mainly acts as the translator of the network. Another name of the presentation layer is the Syntax layer.
The primary goal of this layer is to take care of the syntax and semantics of the information exchanged between two communicating systems. The presentation layer takes care that the data is sent in such a way that the receiver will understand the information(data) and will be able to use the data. Languages(syntax) can be different between the two communicating systems. Under this condition, the presentation layer plays a role as translator.
In order to make it possible for computers with different data representations to communicate, the data structures to be exchanged can be defined in an abstract way. The presentation layer manages these abstract data structures and allows higher-level data structures(eg: banking records), to be defined and exchanged.

We can say that the presentation layer may represent or encode the data in various ways (like data compression, data encryption). But the receiving device mainly decodes or converts the encoded message into its original form.
For the same data, the sender and receiver must need to agree upon a messaging format that is commonly known as the Presentation format.
Also, the presentation layer is a part of the operating system that mainly converts the data from one presentation format to another presentation format.
Protocols used at the Presentation layer
Given below are some of the protocols used at the presentation layer:
AFP(Apple filling protocol)
Secure Socket Layer(SSL)
FTP(file transfer protocol)
Lightweight Presentation Protocol(LPP)
SSH(Secure shell)
Functions of Presentation Layer
Translation: Before being transmitted, the information in the form of characters and numbers should be changed to bitstreams. The presentation layer is responsible for interoperability between encoding methods as different computers use different encoding methods. It translates data between the formats the network requires and the format of the computer.
Encryption: It carries out encryption at the transmitter and decryption at the receiver.
Compression: It carries out data compression to reduce the bandwidth of the data to be transmitted. The primary role of Data compression is to reduce the number of bits to be 0transmitted. It is important in transmitting multimedia such as audio, video, text, etc.
Design Issues with Presentation Layer
To manage and maintain the Syntax and Semantics of the information transmitted.
Encoding data in a standard agreed-upon way. Eg: String, double, date, etc.
Perform Standard Encoding on the wire.
- ← OSI Vs TCP/IP ← PREV
- HTTP Protocol → NEXT →

Presentation Layer
Last Edited
What is the Presentation Layer?
Presentation Layer is the Layer 6 of the seven-layer Open Systems Interconnection (OSI) reference model . The presentation layer structures data that is passed down from the application layer into a format suitable for network transmission. This layer is responsible for data encryption, data compression, character set conversion, interpretation of graphics commands, and so on. The network redirector also functions at this layer.
Presentation Layer functions
- Translation: Before being transmitted, information in the form of characters and numbers should be changed to bit streams. Layer 6 is responsible for interoperability between encoding methods as different computers use different encoding methods. It translates data between the formats the network requires and the format the computer.
- Encryption: Encryption at the transmitter and decryption at the receiver
- Compression: Data compression to reduce the bandwidth of the data to be transmitted. The primary role of data compression is to reduce the number of bits to be transmitted. Multimedia files, such as audio and video, are bigger than text files and compression is more important.
Role of Presentation Layer in the OSI Model
This layer is not always used in network communications because its functions are not always necessary. Translation is only needed if different types of machines need to talk with each other. Encryption is optional in communication. If the information is public there is no need to encrypt and decrypt info. Compression is also optional. If files are small there is no need for compression.
Explaining Layer 6 in video
Most real-world protocol suites, such as TCP/IP , do not use separate presentation layer protocols. This layer is mostly an abstraction in real-world networking.
An example of a program that loosely adheres to layer 6 of OSI is the tool that manages the Hypertext Transfer Protocol (HTTP) — although it’s technically considered an application-layer protocol per the TCP/IP model.
However, HTTP includes presentation layer services within it. HTTP works when the requesting device forwards user requests passed to the web browser onto a web server elsewhere in the network.
It receives a return message from the web server that includes a multipurpose internet mail extensions (MIME) header. The MIME header indicates the type of file – text, video, or audio – that has been received so that an appropriate player utility can be used to present the file to the user.
In short, the presentation layer
Makes sure that data which is being transferred or received should be accurate or clear to all the devices which are there, in a closed network.
- ensures proper formatting and delivery to and from the application layer;
- performs data encryption; and
- manages serialization of data objects.
- Domain Names
- Domain Name Search
- Free Domain Transfer
- .com Domain
- 1 Dollar Domain
- Cheap Domain
- Free Domain
- Buy SSL Certificate
- Website Builder
- Website Platforms
- Website Templates
- Web Design Services
- eCommerce Website Builder
- Local Business Listing
- Web Hosting
- WordPress Hosting
- 1 Dollar Hosting
- Windows Hosting
- Free Website Hosting
- Create Business Email
- HiDrive Cloud Storage
- Microsoft 365 Business
- Cloud Server
- VPS Hosting
- Dedicated Servers
- Rent a Server
- IONOS Cloud
- Business Name Generator
- Logo Creator
- Favicon Generator
- Whois Lookup
- Website Checker
- SSL Checker
- IP Address Check
What is the presentation layer in the OSI model?
The presentation layer is the sixth layer in the OSI model and is responsible for converting different file formats. This allows two systems to communicate. Other tasks carried out by the sixth layer include data compression and encryption.
What is the presentation layer?
What does the presentation layer do, which format does the presentation layer use, presentation layer protocols, skipping the presentation layer.
The presentation layer is the sixth layer of the OSI model. It is primarily used to convert different file formats between the sender and the receiver . The OSI model is a reference model that is used to define communication standards between two devices within a network . The development of this standard began in the 1970s and it was first published at the beginning of the following decade. This standard enables seamless interaction between different technical systems.
The model is made up of a total of seven different layers, all having their own clearly defined tasks. While there are clear boundaries between the layers, the layers interact with each other, with each layer building off the one below it. The different layers are as follows:
- Physical layer
- Data link layer
- Network layer
- Transport layer
- Session layer
- Presentation layer
- Application layer
The presentation layer interacts closely with the application layer, which is located directly above it. The presentation layer’s main task is to present data in such a way that it can be understood and interpreted from both the system sending the data and the system receiving it. After this has been accomplished, the application layer then determines how the data should be structured and what sort of data and values are permissible.
Using these entries, a command set, or an abstract transfer syntax, is then automatically created. The presentation layer now has the task of transferring the data in such a way that it is readable without changing the information contained within it.
The presentation layer is often also responsible for the encryption and decryption of data . The information is first encrypted on the sender’s side and then sent to the receiver in an encrypted state. Keys and encryption methods are then exchanged in the presentation layer. The recipient is then able to decrypt the unreadable data and convert it into a format that can be understood and interpreted.
If data is shown during a transfer, we often use the term transfer syntax. These are separated into the abstract transfer syntax , in which the transferred values are written, and the concrete syntax, which contains a definition of the value coding.
The receiver can only process and understand the data they receive if they receive all of the information from the presentation layer. The most common definition language is Abstract Syntax Notation One (ASN.1) , which is also recommended by the ISO. The ISO is an organization that is responsible for developing international standards in technology, management and manufacturing.
The presentation layer has many different formats. The most common text formats are the ASCII (American Standard Code for Information Interchange) and EBCDIC (Extended Binary-Coded Decimal Interchange Code). The most common image formats are GIF, JPEG and TIFF. Widely used video formats include MIDI, MPEG and QuickTime.
There are many different presentation layer protocols as well as transfer and encryption technologies in the presentation layer. These include:
The tasks which are carried out by the presentation layer are not always necessary for communication between two systems. In instances where both systems use the same formats, data conversion is not necessary. Additionally, encryption and compression are not required for every interaction and can also be carried out in another layer of the OSI model. If this is the case, the presentation layer can be skipped and the application layer (7) can communicate directly with the session layer (5) instead .
- Encyclopedia
Build or host a website, launch a server, or store your data and more with our most popular products for less.

This article explains the Open Systems Interconnection (OSI) model and the 7 layers of networking, in plain English.
The OSI model is a conceptual framework that is used to describe how a network functions. In plain English, the OSI model helped standardize the way computer systems send information to each other.
Learning networking is a bit like learning a language - there are lots of standards and then some exceptions. Therefore, it’s important to really understand that the OSI model is not a set of rules. It is a tool for understanding how networks function.
Once you learn the OSI model, you will be able to further understand and appreciate this glorious entity we call the Internet, as well as be able to troubleshoot networking issues with greater fluency and ease.
All hail the Internet!
Prerequisites
You don’t need any prior programming or networking experience to understand this article. However, you will need:
- Basic familiarity with common networking terms (explained below)
- A curiosity about how things work :)
Learning Objectives
Over the course of this article, you will learn:
- What the OSI model is
- The purpose of each of the 7 layers
- The problems that can happen at each of the 7 layers
- The difference between TCP/IP model and the OSI model
Common Networking Terms
Here are some common networking terms that you should be familiar with to get the most out of this article. I’ll use these terms when I talk about OSI layers next.
A node is a physical electronic device hooked up to a network, for example a computer, printer, router, and so on. If set up properly, a node is capable of sending and/or receiving information over a network.
Nodes may be set up adjacent to one other, wherein Node A can connect directly to Node B, or there may be an intermediate node, like a switch or a router, set up between Node A and Node B.
Typically, routers connect networks to the Internet and switches operate within a network to facilitate intra-network communication. Learn more about hub vs. switch vs. router.
Here's an example:
For the nitpicky among us (yep, I see you), host is another term that you will encounter in networking. I will define a host as a type of node that requires an IP address. All hosts are nodes, but not all nodes are hosts. Please Tweet angrily at me if you disagree.
Links connect nodes on a network. Links can be wired, like Ethernet, or cable-free, like WiFi.
Links to can either be point-to-point, where Node A is connected to Node B, or multipoint, where Node A is connected to Node B and Node C.
When we’re talking about information being transmitted, this may also be described as a one-to-one vs. a one-to-many relationship.
A protocol is a mutually agreed upon set of rules that allows two nodes on a network to exchange data.
“A protocol defines the rules governing the syntax (what can be communicated), semantics (how it can be communicated), and synchronization (when and at what speed it can be communicated) of the communications procedure. Protocols can be implemented on hardware, software, or a combination of both. Protocols can be created by anyone, but the most widely adopted protocols are based on standards.” - The Illustrated Network.
Both wired and cable-free links can have protocols.
While anyone can create a protocol, the most widely adopted protocols are often based on standards published by Internet organizations such as the Internet Engineering Task Force (IETF).
A network is a general term for a group of computers, printers, or any other device that wants to share data.
Network types include LAN, HAN, CAN, MAN, WAN, BAN, or VPN. Think I’m just randomly rhyming things with the word can ? I can ’t say I am - these are all real network types. Learn more here .
Topology describes how nodes and links fit together in a network configuration, often depicted in a diagram. Here are some common network topology types:
A network consists of nodes, links between nodes, and protocols that govern data transmission between nodes.
At whatever scale and complexity networks get to, you will understand what’s happening in all computer networks by learning the OSI model and 7 layers of networking.
What is the OSI Model?
The OSI model consists of 7 layers of networking.
First, what’s a layer?

No, a layer - not a lair . Here there are no dragons.
A layer is a way of categorizing and grouping functionality and behavior on and of a network.
In the OSI model, layers are organized from the most tangible and most physical, to less tangible and less physical but closer to the end user.
Each layer abstracts lower level functionality away until by the time you get to the highest layer. All the details and inner workings of all the other layers are hidden from the end user.
How to remember all the names of the layers? Easy.
- Please | Physical Layer
- Do | Data Link Layer
- Not | Network Layer
- Tell (the) | Transport Layer
- Secret | Session Layer
- Password (to) | Presentation Layer
- Anyone | Application Layer
Keep in mind that while certain technologies, like protocols, may logically “belong to” one layer more than another, not all technologies fit neatly into a single layer in the OSI model. For example, Ethernet, 802.11 (Wifi) and the Address Resolution Protocol (ARP) procedure operate on >1 layer.
The OSI is a model and a tool, not a set of rules.
OSI Layer 1
Layer 1 is the physical layer . There’s a lot of technology in Layer 1 - everything from physical network devices, cabling, to how the cables hook up to the devices. Plus if we don’t need cables, what the signal type and transmission methods are (for example, wireless broadband).
Instead of listing every type of technology in Layer 1, I’ve created broader categories for these technologies. I encourage readers to learn more about each of these categories:
- Nodes (devices) and networking hardware components. Devices include hubs, repeaters, routers, computers, printers, and so on. Hardware components that live inside of these devices include antennas, amplifiers, Network Interface Cards (NICs), and more.
- Device interface mechanics. How and where does a cable connect to a device (cable connector and device socket)? What is the size and shape of the connector, and how many pins does it have? What dictates when a pin is active or inactive?
- Functional and procedural logic. What is the function of each pin in the connector - send or receive? What procedural logic dictates the sequence of events so a node can start to communicate with another node on Layer 2?
- Cabling protocols and specifications. Ethernet (CAT), USB, Digital Subscriber Line (DSL) , and more. Specifications include maximum cable length, modulation techniques, radio specifications, line coding, and bits synchronization (more on that below).
- Cable types. Options include shielded or unshielded twisted pair, untwisted pair, coaxial and so on. Learn more about cable types here .
- Signal type. Baseband is a single bit stream at a time, like a railway track - one-way only. Broadband consists of multiple bit streams at the same time, like a bi-directional highway.
- Signal transmission method (may be wired or cable-free). Options include electrical (Ethernet), light (optical networks, fiber optics), radio waves (802.11 WiFi, a/b/g/n/ac/ax variants or Bluetooth). If cable-free, then also consider frequency: 2.5 GHz vs. 5 GHz. If it’s cabled, consider voltage. If cabled and Ethernet, also consider networking standards like 100BASE-T and related standards.
The data unit on Layer 1 is the bit.
A bit the smallest unit of transmittable digital information. Bits are binary, so either a 0 or a 1. Bytes, consisting of 8 bits, are used to represent single characters, like a letter, numeral, or symbol.
Bits are sent to and from hardware devices in accordance with the supported data rate (transmission rate, in number of bits per second or millisecond) and are synchronized so the number of bits sent and received per unit of time remains consistent (this is called bit synchronization). The way bits are transmitted depends on the signal transmission method.
Nodes can send, receive, or send and receive bits. If they can only do one, then the node uses a simplex mode. If they can do both, then the node uses a duplex mode. If a node can send and receive at the same time, it’s full-duplex – if not, it’s just half-duplex.
The original Ethernet was half-duplex. Full-duplex Ethernet is an option now, given the right equipment.
How to Troubleshoot OSI Layer 1 Problems
Here are some Layer 1 problems to watch out for:
- Defunct cables, for example damaged wires or broken connectors
- Broken hardware network devices, for example damaged circuits
- Stuff being unplugged (...we’ve all been there)
If there are issues in Layer 1, anything beyond Layer 1 will not function properly.
Layer 1 contains the infrastructure that makes communication on networks possible.
It defines the electrical, mechanical, procedural, and functional specifications for activating, maintaining, and deactivating physical links between network devices. - Source
Fun fact: deep-sea communications cables transmit data around the world. This map will blow your mind: https://www.submarinecablemap.com/
And because you made it this far, here’s a koala:

OSI Layer 2
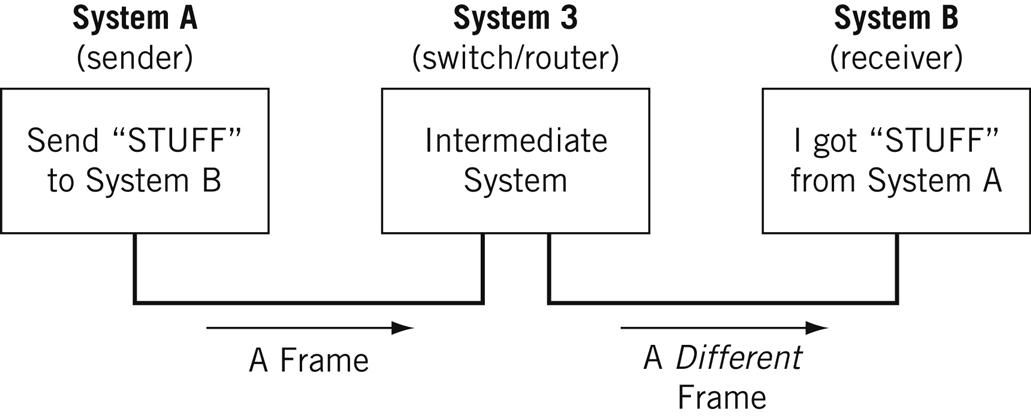
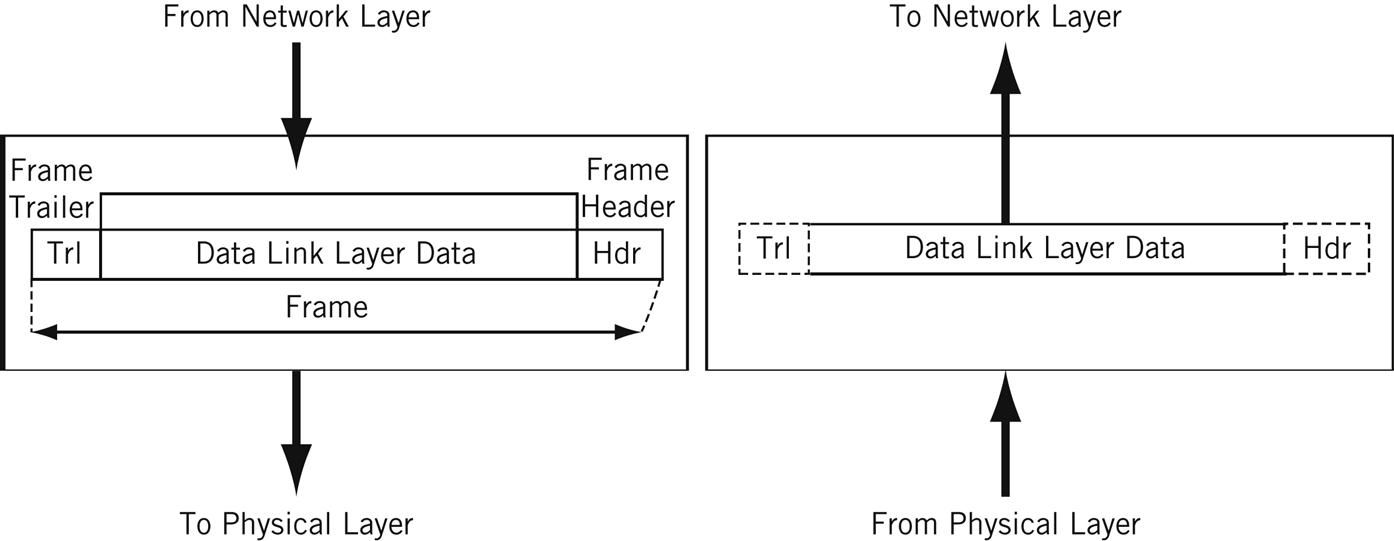
Layer 2 is the data link layer . Layer 2 defines how data is formatted for transmission, how much data can flow between nodes, for how long, and what to do when errors are detected in this flow.
In more official tech terms:
- Line discipline. Who should talk for how long? How long should nodes be able to transit information for?
- Flow control. How much data should be transmitted?
- Error control - detection and correction . All data transmission methods have potential for errors, from electrical spikes to dirty connectors. Once Layer 2 technologies tell network administrators about an issue on Layer 2 or Layer 1, the system administrator can correct for those errors on subsequent layers. Layer 2 is mostly concerned with error detection, not error correction. ( Source )
There are two distinct sublayers within Layer 2:
- Media Access Control (MAC): the MAC sublayer handles the assignment of a hardware identification number, called a MAC address, that uniquely identifies each device on a network. No two devices should have the same MAC address. The MAC address is assigned at the point of manufacturing. It is automatically recognized by most networks. MAC addresses live on Network Interface Cards (NICs). Switches keep track of all MAC addresses on a network. Learn more about MAC addresses on PC Mag and in this article . Learn more about network switches here .
- Logical Link Control (LLC): the LLC sublayer handles framing addressing and flow control. The speed depends on the link between nodes, for example Ethernet or Wifi.
The data unit on Layer 2 is a frame .
Each frame contains a frame header, body, and a frame trailer:
- Header: typically includes MAC addresses for the source and destination nodes.
- Body: consists of the bits being transmitted.
- Trailer: includes error detection information. When errors are detected, and depending on the implementation or configuration of a network or protocol, frames may be discarded or the error may be reported up to higher layers for further error correction. Examples of error detection mechanisms: Cyclic Redundancy Check (CRC) and Frame Check Sequence (FCS). Learn more about error detection techniques here .
Typically there is a maximum frame size limit, called an Maximum Transmission Unit, MTU. Jumbo frames exceed the standard MTU, learn more about jumbo frames here .
How to Troubleshoot OSI Layer 2 Problems
Here are some Layer 2 problems to watch out for:
- All the problems that can occur on Layer 1
- Unsuccessful connections (sessions) between two nodes
- Sessions that are successfully established but intermittently fail
- Frame collisions
The Data Link Layer allows nodes to communicate with each other within a local area network. The foundations of line discipline, flow control, and error control are established in this layer.
OSI Layer 3
Layer 3 is the network layer . This is where we send information between and across networks through the use of routers. Instead of just node-to-node communication, we can now do network-to-network communication.
Routers are the workhorse of Layer 3 - we couldn’t have Layer 3 without them. They move data packets across multiple networks.
Not only do they connect to Internet Service Providers (ISPs) to provide access to the Internet, they also keep track of what’s on its network (remember that switches keep track of all MAC addresses on a network), what other networks it’s connected to, and the different paths for routing data packets across these networks.
Routers store all of this addressing and routing information in routing tables.
Here’s a simple example of a routing table:
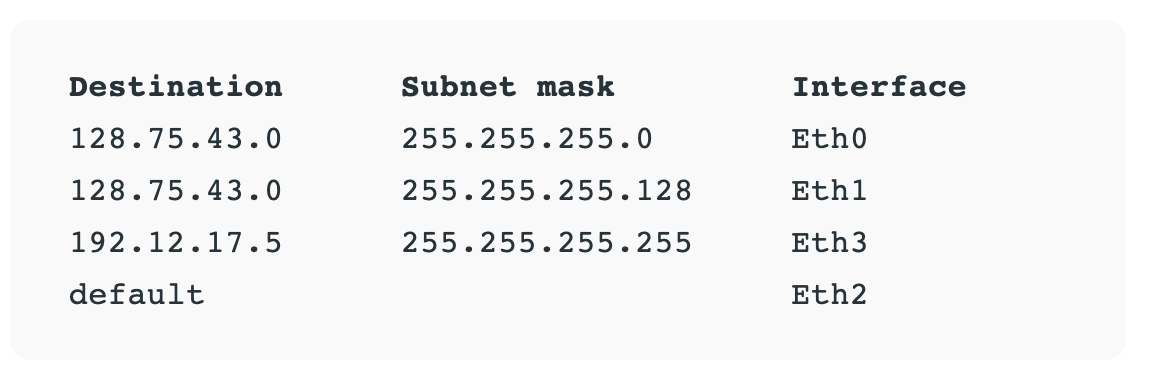
The data unit on Layer 3 is the data packet . Typically, each data packet contains a frame plus an IP address information wrapper. In other words, frames are encapsulated by Layer 3 addressing information.
The data being transmitted in a packet is also sometimes called the payload . While each packet has everything it needs to get to its destination, whether or not it makes it there is another story.
Layer 3 transmissions are connectionless, or best effort - they don't do anything but send the traffic where it’s supposed to go. More on data transport protocols on Layer 4.
Once a node is connected to the Internet, it is assigned an Internet Protocol (IP) address, which looks either like 172.16. 254.1 (IPv4 address convention) or like 2001:0db8:85a3:0000:0000:8a2e:0370:7334 (IPv6 address convention). Routers use IP addresses in their routing tables.
IP addresses are associated with the physical node’s MAC address via the Address Resolution Protocol (ARP), which resolves MAC addresses with the node’s corresponding IP address.
ARP is conventionally considered part of Layer 2, but since IP addresses don’t exist until Layer 3, it’s also part of Layer 3.
How to Troubleshoot OSI Layer 3 Problems
Here are some Layer 3 problems to watch out for:
- All the problems that can crop up on previous layers :)
- Faulty or non-functional router or other node
- IP address is incorrectly configured
Many answers to Layer 3 questions will require the use of command-line tools like ping , trace , show ip route , or show ip protocols . Learn more about troubleshooting on layer 1-3 here .
The Network Layer allows nodes to connect to the Internet and send information across different networks.
OSI Layer 4
Layer 4 is the transport layer . This where we dive into the nitty gritty specifics of the connection between two nodes and how information is transmitted between them. It builds on the functions of Layer 2 - line discipline, flow control, and error control.
This layer is also responsible for data packet segmentation, or how data packets are broken up and sent over the network.
Unlike the previous layer, Layer 4 also has an understanding of the whole message, not just the contents of each individual data packet. With this understanding, Layer 4 is able to manage network congestion by not sending all the packets at once.
The data units of Layer 4 go by a few names. For TCP, the data unit is a packet. For UDP, a packet is referred to as a datagram. I’ll just use the term data packet here for the sake of simplicity.
Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are two of the most well-known protocols in Layer 4.
TCP, a connection-oriented protocol, prioritizes data quality over speed.
TCP explicitly establishes a connection with the destination node and requires a handshake between the source and destination nodes when data is transmitted. The handshake confirms that data was received. If the destination node does not receive all of the data, TCP will ask for a retry.
TCP also ensures that packets are delivered or reassembled in the correct order. Learn more about TCP here .
UDP, a connectionless protocol, prioritizes speed over data quality. UDP does not require a handshake, which is why it’s called connectionless.
Because UDP doesn’t have to wait for this acknowledgement, it can send data at a faster rate, but not all of the data may be successfully transmitted and we’d never know.
If information is split up into multiple datagrams, unless those datagrams contain a sequence number, UDP does not ensure that packets are reassembled in the correct order. Learn more about UDP here .
TCP and UDP both send data to specific ports on a network device, which has an IP address. The combination of the IP address and the port number is called a socket.
Learn more about sockets here .
Learn more about the differences and similarities between these two protocols here .
How to Troubleshoot OSI Layer 4 Problems
Here are some Layer 4 problems to watch out for:
- Blocked ports - check your Access Control Lists (ACL) & firewalls
- Quality of Service (QoS) settings. QoS is a feature of routers/switches that can prioritize traffic, and they can really muck things up. Learn more about QoS here .
The Transport Layer provides end-to-end transmission of a message by segmenting a message into multiple data packets; the layer supports connection-oriented and connectionless communication.
OSI Layer 5
Layer 5 is the session layer . This layer establishes, maintains, and terminates sessions.
A session is a mutually agreed upon connection that is established between two network applications. Not two nodes! Nope, we’ve moved on from nodes. They were so Layer 4.
Just kidding, we still have nodes, but Layer 5 doesn’t need to retain the concept of a node because that’s been abstracted out (taken care of) by previous layers.
So a session is a connection that is established between two specific end-user applications. There are two important concepts to consider here:
- Client and server model: the application requesting the information is called the client, and the application that has the requested information is called the server.
- Request and response model: while a session is being established and during a session, there is a constant back-and-forth of requests for information and responses containing that information or “hey, I don’t have what you’re requesting.”
Sessions may be open for a very short amount of time or a long amount of time. They may fail sometimes, too.
Depending on the protocol in question, various failure resolution processes may kick in. Depending on the applications/protocols/hardware in use, sessions may support simplex, half-duplex, or full-duplex modes.
Examples of protocols on Layer 5 include Network Basic Input Output System (NetBIOS) and Remote Procedure Call Protocol (RPC), and many others.
From here on out (layer 5 and up), networks are focused on ways of making connections to end-user applications and displaying data to the user.
How to Troubleshoot OSI Layer 5 Problems
Here are some Layer 5 problems to watch out for:
- Servers are unavailable
- Servers are incorrectly configured, for example Apache or PHP configs
- Session failure - disconnect, timeout, and so on.
The Session Layer initiates, maintains, and terminates connections between two end-user applications. It responds to requests from the presentation layer and issues requests to the transport layer.
OSI Layer 6
Layer 6 is the presentation layer . This layer is responsible for data formatting, such as character encoding and conversions, and data encryption.
The operating system that hosts the end-user application is typically involved in Layer 6 processes. This functionality is not always implemented in a network protocol.
Layer 6 makes sure that end-user applications operating on Layer 7 can successfully consume data and, of course, eventually display it.
There are three data formatting methods to be aware of:
- American Standard Code for Information Interchange (ASCII): this 7-bit encoding technique is the most widely used standard for character encoding. One superset is ISO-8859-1, which provides most of the characters necessary for languages spoken in Western Europe.
- Extended Binary-Coded Decimal Interchange Code (EBDCIC): designed by IBM for mainframe usage. This encoding is incompatible with other character encoding methods.
- Unicode: character encodings can be done with 32-, 16-, or 8-bit characters and attempts to accommodate every known, written alphabet.
Learn more about character encoding methods in this article , and also here .
Encryption: SSL or TLS encryption protocols live on Layer 6. These encryption protocols help ensure that transmitted data is less vulnerable to malicious actors by providing authentication and data encryption for nodes operating on a network. TLS is the successor to SSL.
How to Troubleshoot OSI Layer 6 Problems
Here are some Layer 6 problems to watch out for:
- Non-existent or corrupted drivers
- Incorrect OS user access level
The Presentation Layer formats and encrypts data.
OSI Layer 7
Layer 7 is the application layer .
True to its name, this is the layer that is ultimately responsible for supporting services used by end-user applications. Applications include software programs that are installed on the operating system, like Internet browsers (for example, Firefox) or word processing programs (for example, Microsoft Word).
Applications can perform specialized network functions under the hood and require specialized services that fall under the umbrella of Layer 7.
Electronic mail programs, for example, are specifically created to run over a network and utilize networking functionality, such as email protocols, which fall under Layer 7.
Applications will also control end-user interaction, such as security checks (for example, MFA), identification of two participants, initiation of an exchange of information, and so on.
Protocols that operate on this level include File Transfer Protocol (FTP), Secure Shell (SSH), Simple Mail Transfer Protocol (SMTP), Internet Message Access Protocol (IMAP), Domain Name Service (DNS), and Hypertext Transfer Protocol (HTTP).
While each of these protocols serve different functions and operate differently, on a high level they all facilitate the communication of information. ( Source )
How to Troubleshoot OSI Layer 7 Problems
Here are some Layer 7 problems to watch out for:
- All issues on previous layers
- Incorrectly configured software applications
- User error (... we’ve all been there)
The Application Layer owns the services and functions that end-user applications need to work. It does not include the applications themselves.
Our Layer 1 koala is all grown up.

Learning check - can you apply makeup to a koala?
Don’t have a koala?
Well - answer these questions instead. It’s the next best thing, I promise.
- What is the OSI model?
- What are each of the layers?
- How could I use this information to troubleshoot networking issues?
Congratulations - you’ve taken one step farther to understanding the glorious entity we call the Internet.
Learning Resources
Many, very smart people have written entire books about the OSI model or entire books about specific layers. I encourage readers to check out any O’Reilly-published books about the subject or about network engineering in general.
Here are some resources I used when writing this article:
- The Illustrated Network, 2nd Edition
- Protocol Data Unit (PDU): https://www.geeksforgeeks.org/difference-between-segments-packets-and-frames/
- Troubleshooting Along the OSI Model: https://www.pearsonitcertification.com/articles/article.aspx?p=1730891
- The OSI Model Demystified: https://www.youtube.com/watch?v=HEEnLZV2wGI
- OSI Model for Dummies: https://www.dummies.com/programming/networking/layers-in-the-osi-model-of-a-computer-network/
Chloe Tucker is an artist and computer science enthusiast based in Portland, Oregon. As a former educator, she's continuously searching for the intersection of learning and teaching, or technology and art. Reach out to her on Twitter @_chloetucker and check out her website at chloe.dev .
Read more posts .
If you read this far, thank the author to show them you care. Say Thanks
Learn to code for free. freeCodeCamp's open source curriculum has helped more than 40,000 people get jobs as developers. Get started
Presentation layer and Session layer of the OSI model
There are two popular networking models: the OSI layers model and the TCP/IP layers model. The presentation layer and session layer exist only in the OSI layers models. The TCP/IP layers model merges them into the application layer.
The Presentation Layer
The presentation layer is the sixth layer of the OSI Reference model. It defines how data and information is transmitted and presented to the user. It translates data and format code in such a way that it is correctly used by the application layer.
It identifies the syntaxes that different applications use and formats data using those syntaxes. For example, a web browser receives a web page from a web server in the HTML language. HTML language includes many tags and markup that have no meaning for the end user but they have special meaning for the web browser. the web browser uses the presentation layer's logic to read those syntaxes and format data in such a way the web server wants it to be present to the user.

On the sender device, it encapsulates and compresses data before sending it to the network to increase the speed and security of the network. On the receiver device, it de-encapsulates and decompresses data before presenting it to the user.
Examples of the presentation layer
Example standards for representing graphical information: JPEG, GIF, JPEG, and TIFF.
Example standards for representing audio information: WAV, MIDI, MP3.
Example standards for representing video information: WMV, MOV, MP4, MPEG.
Example standards for representing text information: doc, xls, txt, pdf.

Functions of the presentation layer
- It formats and presents data and information.
- It encrypts and compresses data before giving it to the session layer.
- It de-encrypts and decompresses the encrypted and compressed data it receives from the session layer.
Session layer
The session layer is the fifth layer of the OSI layers model. It is responsible for initiating, establishing, managing, and terminating sessions between the local application and the remote applications.
It defines standards for three modes of communication: full duplex, half-duplex, and simplex.

In the full duplex mode, both devices can send and receive data simultaneously. The internet connection is an example of the full duplex mode.
In the half duplex mode, only one device can send data at a time. A telephone conversation is an example of the half-duplex mode.
In the simplex mode, only one device can send data. A radio broadcast is an example of the simplex mode.
Functions of the session layer
- It is responsible for terminating sessions, creating checkpoints, and recovering data when sessions are interrupted.
- It opens and maintains logical communication channels between network applications running on the local host and network applications running on the remote host.
- If a network application uses an authentication mechanism before it opens a logical communication channel (session) with the remote host, it handles the authentication process.
Examples of the session layer
Structure Query Language (SQL), Remote Procedure Call (RPC), and Network File System (NFS) are examples of the session layer.
By ComputerNetworkingNotes Updated on 2023-10-30 05:30:01 IST
ComputerNetworkingNotes CCNA Study Guide Presentation layer and Session layer of the OSI model
We do not accept any kind of Guest Post. Except Guest post submission, for any other query (such as adverting opportunity, product advertisement, feedback, suggestion, error reporting and technical issue) or simply just say to hello mail us [email protected]

How-To Geek
The 7 osi networking layers explained.
The Open Systems Interconnection (OSI) networking model defines a conceptual framework for communications between computer systems.
Quick Links
- Physical Layer
- Data Link Layer
- Network Layer
- Transport Layer
- Session Layer
- Presentation Layer
- Application Layer
The Open Systems Interconnection (OSI) networking model defines a conceptual framework for communications between computer systems. The model is an ISO standard which identifies seven fundamental networking layers, from the physical hardware up to high-level software applications.
Each layer in the model handles a specific networking function. The standard helps administrators to visualize networks, isolate problems, and understand the use cases for new technologies. Many network equipment vendors advertise the OSI layer that their products are designed to slot into.
OSI was adopted as an international standard in 1984. It remains relevant today despite the changes to network implementation that have occurred since first publication. Cloud, edge, and IoT can all be accommodated within the model.
In this article, we'll explain each of the seven OSI layers in turn. We'll start from the lowest level, labelled as Layer 1.
1. Physical Layer
All networking begins with physical equipment. This layer encapsulates the hardware involved in the communications, such as switches and cables. Data is transferred as a stream of binary digits - 0 or 1 - that the hardware prepares from input it's been fed. The physical layer specifies the electrical signals that are used to encode the data over the wire, such as a 5-volt pulse to indicate a binary "1."
Errors in the physical layer tend to result in data not being transferred at all. There could be a break in the connection due to a missing plug or incorrect power supply. Problems can also arise when two components disagree on the physical encoding of data values. In the case of wireless connections, a weak signal can lead to bit loss during transmission.
2. Data Link Layer
The model's second layer concerns communication between two devices that are directly connected to each other in the same network. It's responsible for establishing a link that allows data to be exchanged using an agreed protocol. Many network switches operate at Layer 2.
The data link layer will eventually pass bits to the physical layer. As it sits above the hardware, the data link layer can perform basic error detection and correction in response to physical transfer issues. There are two sub-layers that define these responsibilities: Logical Link Control (LLC) that handles frame synchronization and error detection, and Media Access Control (MAC) which uses MAC addresses to constrain how devices acquire permission to transfer data.
3. Network Layer
The network layer is the first level to support data transfer between two separately maintained networks. It's redundant in situations where all your devices exist on the same network.
Data that comes to the network layer from higher levels is first broken up into packets suitable for transmission. Packets received from the remote network in response are reassembled into usable data.
The network layer is where several important protocols are first encountered. These include IP (for determining the path to a destination), ICMP, routing, and virtual LAN. Together these mechanisms facilitate inter-network communications with a familiar degree of usability. However operations at this level aren't necessarily reliable: messages aren't required to succeed and may not necessarily be retried.
4. Transport Layer
The transport layer provides higher-level abstractions for coordinating data transfers between devices. Transport controllers determine where data will be sent and the rate it should be transferred at.
Layer 4 is where TCP and UDP are implemented, providing the port numbers that allow devices to expose multiple communication channels. Load balancing is often situated at Layer 4 as a result, allowing traffic to be routed between ports on a target device.
Transport mechanisms are expected to guarantee successful communication. Stringent error controls are applied to recover from packet loss and retry failed transfers. Flow control is enforced so the sender doesn't overwhelm the remote device by sending data more quickly than the available bandwidth permits.
5. Session Layer
Layer 5 creates ongoing communication sessions between two devices. Sessions are used to negotiate new connections, agree on their duration, and gracefully close down the connection once the data exchange is complete. This layer ensures that sessions remain open long enough to transfer all the data that's being sent.
Checkpoint control is another responsibility that's held by Layer 5. Sessions can define checkpoints to facilitate progress updates and resumable transmissions. A new checkpoint could be set every few megabytes for a file upload, allowing the sender to continue from a particular point if the transfer gets interrupted.
Many significant protocols operate at Layer 5 including authentication and logon technologies such as LDAP and NetBIOS. These establish semi-permanent communication channels for managing an end user session on a specific device.
6. Presentation Layer
The presentation layer handles preparation of data for the application layer that comes next in the model. After data has made it up from the hardware, through the data link, and across the transport, it's almost ready to be consumed by high-level components. The presentation layer completes the process by performing any formatting tasks that may be required.
Decryption, decoding, and decompression are three common operations found at this level. The presentation layer processes received data into formats that can be eventually utilized by a client application. Similarly, outward-bound data is reformatted into compressed and encrypted structures that are suitable for network transmission.
TLS is one major technology that's part of the presentation layer. Certificate verification and data decryption is handled before requests reach the network client, allowing information to be consumed with confidence that it's authentic.
7. Application Layer
The application layer is the top of the stack. It represents the functionality that's perceived by network end users. Applications in the OSI model provide a convenient end-to-end interface to facilitate complete data transfers, without making you think about hardware, data links, sessions, and compression.
Despite its name, this layer doesn't relate to client-side software such as your web browser or email client. An application in OSI terms is a protocol that caters for the complete communication of complex data through layers 1-6.
HTTP, FTP, DHCP, DNS, and SSH all exist at the application layer. These are high-level mechanisms which permit direct transfers of user data between an origin device and a remote server. You only need minimal knowledge of the workings of the other layers.
The seven OSI layers describe the transfer of data through computer networks. Understanding the functions and responsibilities of each layer can help you identify the source of problems and assess the intended use case for new components.
OSI is an abstract model that doesn't directly map to the specific networking implementations commonly used today. As an example, the TCP/IP protocol works on its own simpler system of four layers: Network Access, Internet, Transport, and Application. These abstract and absorb the equivalent OSI layers: the application layer spans OSI L5 to L7, while L1 and L2 are combined in TCP/IP's concept of Network Access.
OSI remains applicable despite its lack of direct real-world application. It's been around so long that it's widely understood among administrators from all backgrounds. Its relatively high level of abstraction has also ensured it's remained relevant in the face of new networking paradigms, many of which have targeted Layer 3 and above. An awareness of the seven layers and their responsibilities can still help you appreciate the flow of data through a network while uncovering integration opportunities for new components.

Computer Network
- Operating Systems
- Computer Fundamentals
- Interview Q
Physical Layer
Data link layer, network layer, routing algorithm, transport layer, application layer, application protocols, network security.
Interview Questions
- Send your Feedback to [email protected]
Help Others, Please Share

Learn Latest Tutorials
Transact-SQL
Reinforcement Learning
R Programming
React Native
Python Design Patterns
Python Pillow
Python Turtle
Preparation

Verbal Ability

Company Questions
Trending Technologies
Artificial Intelligence
Cloud Computing
Data Science
Machine Learning
B.Tech / MCA
Data Structures
Operating System
Compiler Design
Computer Organization
Discrete Mathematics
Ethical Hacking
Computer Graphics
Software Engineering
Web Technology
Cyber Security
C Programming
Control System
Data Mining
Data Warehouse

Session and Presentation layers in the OSI model
Alessandro Maggio
- December 29, 2016

Share This Post
Session and presentation layers in the OSI stack can be considered fancy layers , as they are known only by a small part of Network Engineers. This is probably because all their features blend either in transport-layer protocols or in application-layer protocols. However, with this article, you will discover all the beauty of these two layers, learning what they do and how they are implemented.
UDP limitations
Back in the CCNA course, we found out that the only place we can see the session and presentation layers truly implemented is when they are based on UDP transport. UDP leaves some room to these two layers (if compared to TCP) because it is extremely simple and lacking features . These features can be then implemented in upper layers individually, adding modularity. Just to refresh your mind, UDP has the following two limitations.
UDP, all by itself, do not order packets, and therefore the receiver cannot guess in which order they were sent originally. Moreover, it is not reliable, what is lost is just lost, no UDP component will trigger a re-transmission. Adding these features, however, would increase the complexity of the algorithm behind UDP running on hosts and will add extra fields in the UDP header sent with every segment. All of that, and specifically the extra bytes added in the segment’s header, is called overhead : the extra amount of information that allows application data to be delivered correctly. Our goal is to obtain the delivery of application data as we want it with the least overhead possible .
In the article about advanced TCP , we already explained the ways we can reduce the TCP overhead using selective ACK and header compression, but all of these complex items cannot reduce the TCP header to the size of a UDP header. Instead, with UDP we follow a different approach: we start from almost no features (only delivery to the correct application using port numbers) and we add the features we need in upper layers.
Session layer
The session layer is the one implementing one-to-one application sessions: it defines the re-transmission of data, the segment ordering method, and control the communication in general. All these features are covered by TCP for applications using that transport protocol, but applications that leverage UDP have to implement these features autonomously (within the application) or rely on an extra protocol specifically sitting at the session layer. Many applications (such as TFTP) rely on the first option, while the second alternative is the privileged one for VoIP. For VoIP traffic, the protocol we rely on for the session is the Real-time Transport Protocol (RTP) . As we are talking about applications using UDP as their underlying transport, spending some time on RTP is certainly well-worth since Voice and Video are the king applications among all UDP-based applications .
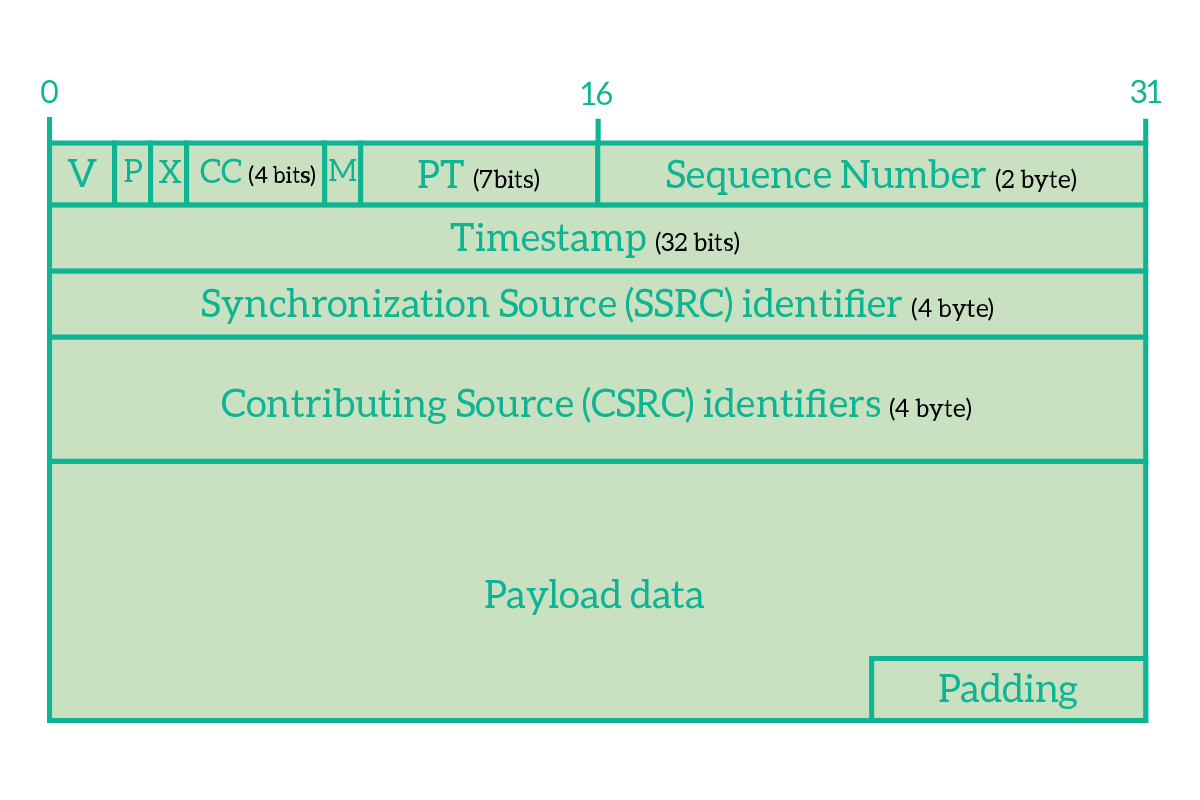
The RTP header in the picture is inserted just after the UDP header, and add extra features such as the reordering of segments and their timing, which are extremely important for an application that must run real-time. Here’s the explanation of its fields.
- Version – Version of RTP, the up-to-date one is version 2
- P (Padding) – Flag used to indicate whether padding is present or not in the segment
- X (Extension) – Flag used to indicate whether extension header is present or not
- CC (CSRC count) – Number of CSRC identifiers contained in the header
- M (Marker) – Flag that, if set, indicates that this segment has some special relevance for the application
- PT (Payload Type) – Indicates the type of RTP payload (e.g. for VoIP/Video stream)
- Sequence number – Used from the receiver to reorder packets, incremented by one each segment sent
- Timestamp – Time the segment was created, used to allow the receiver to play the content of the segment (assuming that it is audio or video) at the proper interval
- SSCS – Synchronization Source Identifier, identifies a stream of UDP/RTP segments
- CSRC – Contributing Source IDs, indicates the source of the audio stream, multiple CSRCs can be specified if there are multiple sources (e.g. in a three-party conference)
- Header extension – extra header, optional and profile-specific
These fields are the minimum needed to allow the transmission and are specifically designed for real-time streams, audio, and video mainly. Looking at the header, you can still find the Sequence number as in TCP, but no acknowledgment number . This is because RTP allows the receiver to reorder segments , but not to arrange a re-transmission. This behavior is purposefully designed this way, as a VoIP call or a video stream needs to be delivered now. In case something is lost, there is no time to re-transmit it, the show must go on. If we re-transmit it, it would arrive too late so there is no point in the retransmission at all. Another interesting field adding a feature UDP is lacking is the timestamp, with that field you can know when the content was generated and reproduce the sound and video at the same interval it was generated. Otherwise, you would have audio and video streams increasing and decreasing speed according to the network connection available.
A question I’ve been asked several times when talking about reordering packets is “How they arrive in the wrong order in the first place?” and this is surely a good question. The answer has a lot to do with routing , so it lays at the Network Layer in the OSI Stack. Routers work independently from the upper layer protocols and applications, they run based on IP addressing and routes. It might happen that a node fails over the network and traffic takes a different path to avoid falling on the faulty link, or simply a router discovers a better path to a destination. Since all of this happens dynamically, at a given moment the traffic might go over a link and one second later over another. Not all links have the same speed, so it is possible that a segment sent later but over a fast link will arrive before a segment sent previously but on a slow link. Let’s have a look at the following picture.
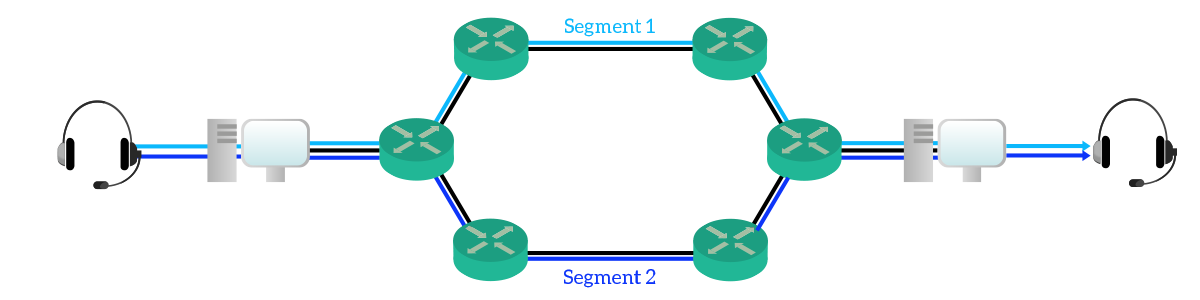
Edge devices (computers, servers) do not know about the network infrastructure, so they just know that there is the possibility that segments are disordered during the transmission by taking different ways. Because of that, they have to implement mechanisms for reordering . Reordering is crucial to almost any application, to transfer a file we need to know the order of its part, and to transfer audio stream we need to know in which order to play the sounds.
Presentation for Real-Time applications
The presentation layer is probably the most mysterious one. This is because almost no application implements it, neither among the UDP applications. What this layer does, is to define how data should be presented to the application. Once again, coming to rescue us we have VoIP and Video stream, the ones leveraging this layer the most. Basically, when you make a VoIP call there are some parameters involved in the audio stream, such as the bitrate or the compression rate just to name a few. To have the smoothest audio stream possible, all the parties involved must agree on how they are going to exchange audio and video. RTP is the common ground that cannot be changed, here we are talking about how to write the payload of the RTP segment. In other words, we are defining the codec.
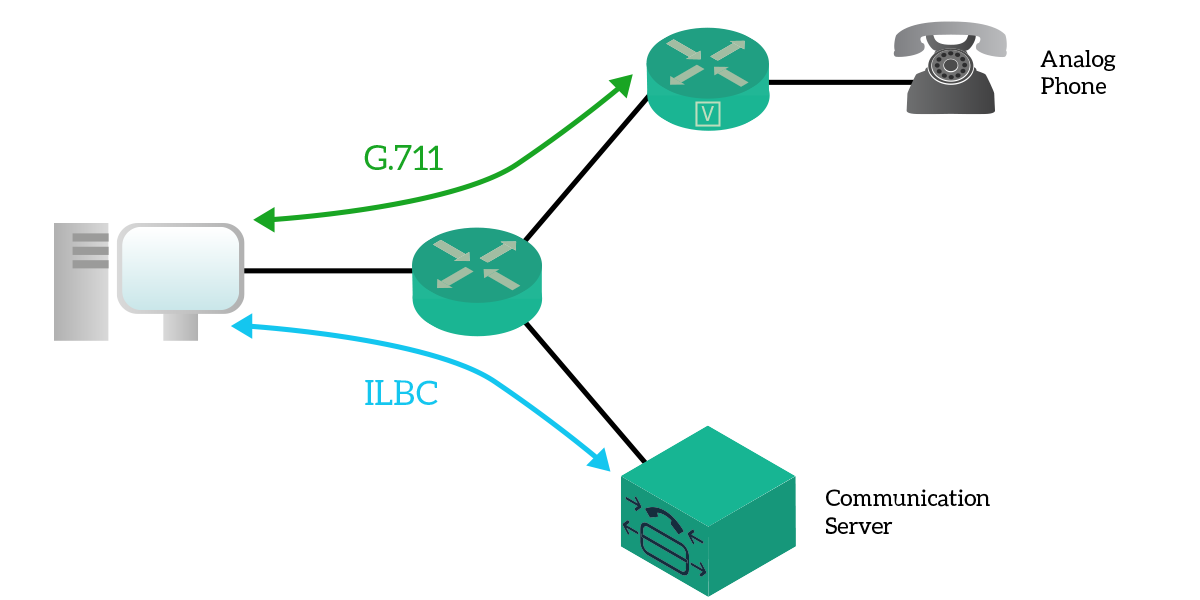
Some codecs may privilege the compression, using less bandwidth but more computational resources, others may use a lot of bandwidth but almost no computational resources or other ones require fewer resources sacrificing audio quality. No choice can be right on all occasions, the best codec for any situation depends on your needs.
Session and presentation layers in the shadow
We now know what these two layers are truly about, but let’s take a moment to check out why they are not famous like the other OSI layers. Even previously we had the chance to understand how there is almost no need to implement them, as their features are covered elsewhere, however it is time to give some examples, as in the following picture.
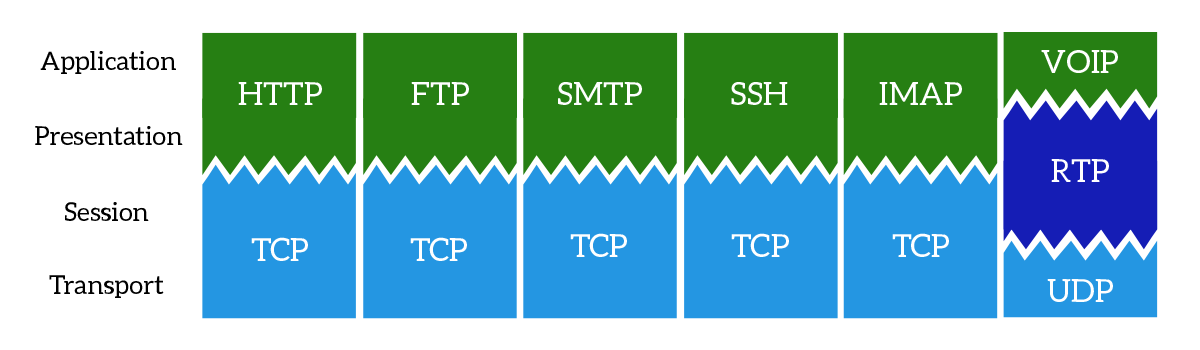
What the picture says is also listed below in a little more detail.
- HTTP (Hyper-Text Transfer Protocol) – Used to transfer web-pages, the session layer is handled by TCP while there is no need for a presentation layer as the information is sent in simple text or raw binary
- FTP (File Transfer Protocol) – Used to transfer files to and from a server, the session layer is handled by TCP while there is no need for a presentation layer as the information is sent in raw binary
- SMTP (Simple Mail Transfer Protocol) – Used to send emails from a server o another, the session layer is handled by TCP while there is no need for a presentation layer as the information is sent in simple text
- SSH (Secure Shell) – Used to connect to a remote device and control it via textual commands using encryption, the session layer is handled by TCP while there is no need for a presentation layer as the information is sent in simple text
- IMAP (Internet Message Access Protocol) – Used to connect to an email server and check emails, the session layer is handled by TCP while there is no need for a presentation layer as the information is sent in simple text
- VoIP (Voice over IP) – This is not a real protocol, but instead a type of application, RTP manages the session layer while the presentation layer exists and is managed at the application layer
This article was really lightweight, as UDP is. With this knowledge, you know all the differences between UDP and TCP and you are ready to discuss the technologies implemented in a network to support modern applications. In the following articles, we will start to see some application layer protocols before we can dive into the configuration items.
Never Stop Learning...
6 amazing generative ai use cases for the real world, 6 amazing large business ideas (+ come up with your own), don't fail the ccna exam, failing the ccna exam equals wasting $300. don't do that, be prepared instead., together with our free course, we offer a companion book with questions and answers. and it's only $27.50 if you are following the course..
Join the Newsletter to Get Ahead
Revolutionary tips to get ahead with technology directly in your inbox..
2016-12-29T16:30:49+00:00
Unspecified
Free CCNA Course
Want Visibility from Tech Professionals?
If you feel like sharing your knowledge, we are open to guest posting - and it's free. find out more now..

Accessibility
Free courses.
- Bahasa Indonesia
- Sign out of AWS Builder ID
- AWS Management Console
- Account Settings
- Billing & Cost Management
- Security Credentials
- AWS Personal Health Dashboard
- Support Center
- Expert Help
- Knowledge Center
- AWS Support Overview
- AWS re:Post
- What is Cloud Computing?
- Cloud Computing Concepts Hub
- Networking & Content Delivery
What is OSI Model?

What is the OSI Model?
The Open Systems Interconnection (OSI) model is a conceptual framework that divides network communications functions into seven layers. Sending data over a network is complex because various hardware and software technologies must work cohesively across geographical and political boundaries. The OSI data model provides a universal language for computer networking, so diverse technologies can communicate using standard protocols or rules of communication. Every technology in a specific layer must provide certain capabilities and perform specific functions to be useful in networking. Technologies in the higher layers benefit from abstraction as they can use lower-level technologies without having to worry about underlying implementation details.
Why is the OSI model important?
The layers of the Open Systems Interconnection (OSI) model encapsulate every type of network communication across both software and hardware components. The model was designed to allow two standalone systems to communicate via standardised interfaces or protocols based on the current layer of operation.
The benefits of the OSI model are given next.
Shared understanding of complex systems
Engineers can use the OSI model to organize and model complex networked system architectures. They can separate the operating layer of each system component according to its main functionality. The ability to decompose a system into smaller, manageable parts via abstraction makes it easier for people to conceptualize it as a whole.
Faster research and development
With the OSI reference model, engineers can understand their work better. They know which technological layer (or layers) they’re developing for when they create new, networked systems that need to communicate with each other. Engineers can develop networked systems and take advantage of a series of repeatable processes and protocols.
Flexible standardization
The OSI model does not specify the protocols to use between levels, but rather the tasks that protocols perform. It standardizes network communication development so people can rapidly understand, build, and decompose highly complex systems—all without prior knowledge of the system. It also abstracts details, so engineers don’t require the understanding of every aspect of the model. In modern applications, the lower levels of networking and protocols are abstracted away to simplify system design and development. The following image shows how the OSI model is used in modern application development.

What are the seven layers of the OSI model?
The Open Systems Interconnection (OSI) model was developed by the International Organization for Standardization and others in the late 1970s. It was published in its first form in 1984 as ISO 7498, with the current version being ISO/IEC 7498-1:1994. The seven layers of the model are given next.
Physical layer
The physical layer refers to the physical communication medium and the technologies to transmit data across that medium. At its core, data communication is the transfer of digital and electronic signals through various physical channels like fiber-optic cables, copper cabling, and air. The physical layer includes standards for technologies and metrics closely related with the channels, such as Bluetooth, NFC, and data transmission speeds.
Data link layer
The data link layer refers to the technologies used to connect two machines across a network where the physical layer already exists. It manages data frames, which are digital signals encapsulated into data packets. Flow control and error control of data are often key focuses of the data link layer. Ethernet is an example of a standard at this level. The data link layer is often split into two sub-layers: the Media Access Control (MAC) layer and Logical Link Control (LLC) layer.
Network layer
The network layer is concerned with concepts such as routing, forwarding, and addressing across a dispersed network or multiple connected networks of nodes or machines. The network layer may also manage flow control. Across the internet, the Internet Protocol v4 (IPv4) and IPv6 are used as the main network layer protocols.
Transport layer
The primary focus of the transport layer is to ensure that data packets arrive in the right order, without losses or errors, or can be seamlessly recovered if required. Flow control, along with error control, is often a focus at the transport layer. At this layer, commonly used protocols include the Transmission Control Protocol (TCP), a near-lossless connection-based protocol, and the User Datagram Protocol (UDP), a lossy connectionless protocol. TCP is commonly used where all data must be intact (e.g. file share), whereas UDP is used when retaining all packets is less critical (e.g. video streaming).
Session layer
The session layer is responsible for network coordination between two separate applications in a session. A session manages the beginning and ending of a one-to-one application connection and synchronization conflicts. Network File System (NFS) and Server Message Block (SMB) are commonly used protocols at the session layer.
Presentation layer
The presentation layer is primarily concerned with the syntax of the data itself for applications to send and consume. For example, Hypertext Markup Language (HTML) , JavaScipt Object Notation (JSON) , and Comma Separated Values (CSV) are all modeling languages to describe the structure of data at the presentation layer.
Application layer
The application layer is concerned with the specific type of application itself and its standardized communication methods. For example, browsers can communicate using HyperText Transfer Protocol Secure (HTTPS), and HTTP and email clients can communicate using POP3 (Post Office Protocol version 3) and SMTP (Simple Mail Transfer Protocol).
Not all systems that use the OSI model implement every layer.
How does communication happen in the OSI model?
The layers in the Open Systems Interconnection (OSI) model are designed so that an application can communicate over a network with another application on a different device, no matter the complexity of the application and underlying systems. To do this, various standards and protocols are used to communicate with the layer above or below. Each of the layers is independent and only aware of the interfaces to communicate with the layer above and below it.
By chaining together all these layers and protocols, complex data communications can be sent from one high-level application to another. The process works as follows:
- The sender’s application layer passes data communication down to the next lower layer.
- Each layer adds its own headers and addressing to the data before passing it on.
- Data communication moves down the layers until it is eventually transmitted through the physical medium.
- At the other end of the medium, each layer processes the data according to the relevant headers at that level.
- At the receiver end, data moves up the layer and is gradually unpacked until the application at the other end receives it.
What are alternatives to the OSI model?
Various networking models were used in the past, such as Sequenced Packet Exchange/Internet Packet Exchange (SPX/IPX) and Network Basic Input Output System (NetBIOS). Today, the main alternative to the Open Systems Interconnection (OSI) model is the TCP/IP model.
The TCP/IP model
The TCP/IP model is comprised of five different layers:
- The physical layer
- The data link layer
- The network layer
- The transport layer
- They application layer
While layers like the physical layer, network layer, and application layer appear to map directly to the OSI model, this isn’t quite the case. Instead, the TCP/IP model most accurately maps to the structure and protocols of the internet.
The OSI model remains a popular networking model to describe how networking operates from a holistic perspective for educational purposes. However, the TCP/IP model is now more commonly used in practice.
A note on proprietary protocols and models
It’s important to note that not all internet-based systems and applications follow the TCP/IP model or the OSI model. Similarly, not all offline-based networked systems and applications use the OSI model or any other model.
Both the OSI and TCP/IP models are open standards. They’re designed so that anyone can use them, or further build them out to meet specific requirements.
Organizations also design their own internal, proprietary standards, including protocols and models, that are closed-source and only for use within their systems. Sometimes, they may subsequently release them to the public for interoperability and further community development. An example is s2n-tls, a TLS protocol that was originally a proprietary Amazon Web Services (AWS) protocol but is now open source.
How can AWS meet your computer networking requirements?
AWS helps organizations design, deploy, and scale networked systems and applications with less friction.
We have a robust suite of AWS Networking and Content Delivery offerings. They’re designed to complement and integrate with your internal applications and services, across all levels of network operations. Here are some examples:
- AWS App Mesh provides secure, application-level networking for all your services, with built-in communications monitoring and control
- Amazon CloudFront is a content delivery network (CDN) service built for high performance, security, and developer convenience
- AWS Direct Connect offers a direct connection, which doesn’t touch the internet, from your organization to your AWS resources
- Elastic Load Balancing (ELB) distributes incoming network traffic across AWS targets to improve application scalability
Get started with networked systems and applications on AWS by creating an account today.
Next Steps on AWS
Ending Support for Internet Explorer
Create your address on the web.
- Domain Check
Move your domain name to IONOS.
- Free Domain
Secure site traffic and build trust.
Create your own website easily.
Our experts build your website.
Create your own online store.
Fast, scalable hosting for any website.
Optimized for speed, reliablity and control.
Reach out with your own email address.
Secure and share your data on the go.
Powerful Exchange email and Microsoft's trusted productivity suite.
Pay as you go with your own scalable private server.
- Virtual Private Servers (VPS)
Get enterprise hardware with unlimited traffic
Individually configurable, highly scalable IaaS cloud
- Business Name Generator
- Logo Creator
- Favicon Generator
- Whois Lookup
- Website Checker
- SSL Checker
- IP Address Check
What is the presentation layer in the OSI model?
The presentation layer is the sixth layer in the OSI model and is responsible for converting different file formats. This allows two systems to communicate. Other tasks carried out by the sixth layer include data compression and encryption.
What is the presentation layer?
What does the presentation layer do, which format does the presentation layer use, presentation layer protocols, skipping the presentation layer.
The presentation layer is the sixth layer of the OSI model. It is primarily used to convert different file formats between the sender and the receiver . The OSI model is a reference model that is used to define communication standards between two devices within a network . The development of this standard began in the 1970s and it was officially published at the beginning of the following decade. This standard enables seamless interaction between different technical systems.
The model is made up of a total of seven different layers, all having their own clearly defined tasks. While there are clear boundaries between the layers, the layers interact with each other, with each layer building off the one below it. The different layers are as follows:
- Physical layer
- Data link layer
- Network layer
- Transport layer
- Session layer
- Presentation layer
- Application layer
The presentation layer interacts closely with the application layer, which is located directly above it. The presentation layer’s main task is to present data in such a way that it can be understood and interpreted from both the system sending the data and the system receiving it. After this has been accomplished, the application layer then determines how the data should be structured and what sort of data and values are permissible.
Using these entries, a command set or an abstract transfer syntax is then automatically created. The presentation layer now has the task of transferring the data in such a way that it is readable without changing the information contained within it.
The presentation layer is often also responsible for the encryption and decryption of data . The information is first encrypted on the sender’s side and then sent to the receiver in an encrypted state. Keys and encryption methods are then exchanged in the presentation layer. The recipient is then able to decrypt the unreadable data and convert it into a format that can be understood and interpreted.
If data is shown during a transfer, we often use the term transfer syntax. These are separated into the abstract transfer syntax , in which the transferred values are written, and the concrete syntax, which contains a definition of the value coding.
The receiver can only process and understand the data they receive if they receive all of the information from the presentation layer. The most common definition language is Abstract Syntax Notation One (ASN.1) , which is also recommended by the ISO. The ISO is an organisation that is responsible for developing international standards in technology, management and manufacturing.
The presentation layer has many different formats. The most common text formats are the ASCII (American Standard Code for Information Interchange) and EBCDIC (Extended Binary-Coded Decimal Interchange Code). The most common image formats are GIF, JPEG and TIFF. Widely used video formats include MIDI, MPEG and QuickTime.
There are many different presentation layer protocols as well as transfer and encryption technologies in the presentation layer. These include:
The tasks which are carried out by the presentation layer are not always necessary for communication between two systems. In instances where both systems use the same formats, data conversion is not necessary. Additionally, encryption and compression are not required for every interaction and can also be carried out in another layer of the OSI model. If this is the case, the presentation layer can be skipped and the application layer (7) can communicate directly with the session layer (5) instead .
- Encyclopedia
Get the flexible infrastructure you need to meet any demand, from fully virtualised VPS to scalable cloud solutions.


IMAGES
VIDEO
COMMENTS
Prerequisite : OSI Model. Introduction : Presentation Layer is the 6th layer in the Open System Interconnection (OSI) model. This layer is also known as Translation layer, as this layer serves as a data translator for the network. The data which this layer receives from the Application Layer is extracted and manipulated here as per the required ...
Telnet (Telecommunication Network): Telnet protocol was introduced in 1969, and it offers the command line interface for making communication along with remote device or server. Tox: The Tox protocol is sometimes regarded as part of both the presentation and application layer, and it is used for sending peer-to-peer instant-messaging as well as video calling.
For example, HyperText Transfer Protocol (HTTP), generally regarded as an application-layer protocol, has presentation-layer aspects such as the ability to identify character encoding for proper conversion, which is then done in the application layer. The presentation layer is the lowest layer at which application programmers consider data ...
The presentation layer is the lowest layer at which application programmers consider data structure and presentation, instead of simply sending data in the form of datagrams or packets between hosts. This layer deals with issues of string representation - whether they use the Pascal method (an integer length field followed by the specified ...
The presentation layer in the OSI model has five main functions within the frame of presentation layer protocols. Character Code Translation A character code is a representation of text using a ...
The presentation layer is the sixth layer in the OSI model. Known as a translator, the presentation layer converts data into an accurate, well-defined, standard format after it receives it from the application layer. The converted format varies, however, based on the type of data received. Some formats include:
The presentation layer is the sixth layer of the OSI Reference Model protocol stack, and second from the top. It is different from the other layers in two key respects. First, it has a much more limited and specific function than the other layers; it's actually somewhat easy to describe, hurray! Second, it is used much less often than the other ...
The presentation layer is located at Layer 6 of the OSI model. The tool that manages Hypertext Transfer Protocol ( HTTP) is an example of a program that loosely adheres to the presentation layer of OSI. Although it's technically considered an application-layer protocol per the TCP/IP model, HTTP includes presentation layer services within it.
Also, the presentation layer is a part of the operating system that mainly converts the data from one presentation format to another presentation format. Protocols used at the Presentation layer. Given below are some of the protocols used at the presentation layer: AFP(Apple filling protocol) Secure Socket Layer(SSL) FTP(file transfer protocol ...
Presentation Layer Protocols. Henrik Frystyk, July 94. Presentation Layer Protocols. This section introduces some of the Presentation Layer protocols on the Internet that are related to the World-Wide Web project. The main WWW protocol, Hypertext Transfer Protocol is described in the The HTTP Protocol. The protocols presented are:
Most real-world protocol suites, such as TCP/IP, do not use separate presentation layer protocols. This layer is mostly an abstraction in real-world networking. Layer 6 OSI Model. An example of a program that loosely adheres to layer 6 of OSI is the tool that manages the Hypertext Transfer Protocol (HTTP) — although it's technically ...
The presentation layer translates information in a way that the application layer understands. Likewise, this layer translates information from the application layer to the session layer. Some examples of presentation layer protocols are SSL, HTTP/ HTML (agent), FTP (server), AppleTalk Filing Protocol,Telnet, and so on.
The presentation layer is the sixth layer of the OSI model. It is primarily used to convert different file formats between the sender and the receiver. The OSI model is a reference model that is used to define communication standards between two devices within a network. The development of this standard began in the 1970s and it was first ...
The Session Layer initiates, maintains, and terminates connections between two end-user applications. It responds to requests from the presentation layer and issues requests to the transport layer. OSI Layer 6. Layer 6 is the presentation layer. This layer is responsible for data formatting, such as character encoding and conversions, and data ...
The presentation layer is the sixth layer of the OSI Reference model. It defines how data and information is transmitted and presented to the user. It translates data and format code in such a way that it is correctly used by the application layer. It identifies the syntaxes that different applications use and formats data using those syntaxes.
Data Link Layer. Network Layer. Transport Layer. Session Layer. Presentation Layer. Application Layer. Summary. The Open Systems Interconnection (OSI) networking model defines a conceptual framework for communications between computer systems. The model is an ISO standard which identifies seven fundamental networking layers, from the physical ...
Protocols of the Presentation layer: Independent Computing Architecture (ICA): It is a presentation layer protocol in the OSI model, which was formed by Citrix Systems. It is used for transferring data from server to client. It is a very thin protocol as it does not require much overhead in order to transmit data from the server over to the client.
Session layer. The session layer is the one implementing one-to-one application sessions: it defines the re-transmission of data, the segment ordering method, and control the communication in general. All these features are covered by TCP for applications using that transport protocol, but applications that leverage UDP have to implement these ...
The network layer is concerned with concepts such as routing, forwarding, and addressing across a dispersed network or multiple connected networks of nodes or machines. The network layer may also manage flow control. Across the internet, the Internet Protocol v4 (IPv4) and IPv6 are used as the main network layer protocols. Transport layer
Key functions of the Presentation Layer in the OSI model include: Data Encryption: It securely encrypts data to prevent unauthorized access during transmission. Data Compression: It reduces data ...
The presentation layer is the sixth layer of the OSI model. It is primarily used to convert different file formats between the sender and the receiver. The OSI model is a reference model that is used to define communication standards between two devices within a network. The development of this standard began in the 1970s and it was officially ...
Examples of secure protocols used at the Presentation Layer are Transport Layer Security (TLS) and Secure Sockets Layer (SSL), which encrypt communications between parties. Additionally, the use of robust encryption and decryption mechanisms, such as symmetric and asymmetric key encryption, can help protect against man-in-the-middle and replay ...
Presentation layer protocols: The presentation layer, which is the sixth and most crucial layer in the OSI model, carries out a number of functions that guarantee that data being sent or received ...